Learning Linux For DevOps
Introduction
If you have chosen the DevOps engineering path for your career, Linux system administration skills are a must. Companies run their workloads on Linux on-premise as well as in the cloud. Many developers write software on their Linux laptops and workstations. In this post, I will lay out a plan to master Linux system administration skills. The journey begins with you becoming a Linux desktop user. Gradually, you start using your laptop as a Linux server. Become more productive and create your own labs using virtualization. You will be able to simulate a lot of Linux infrastructure scenarios on your laptop.
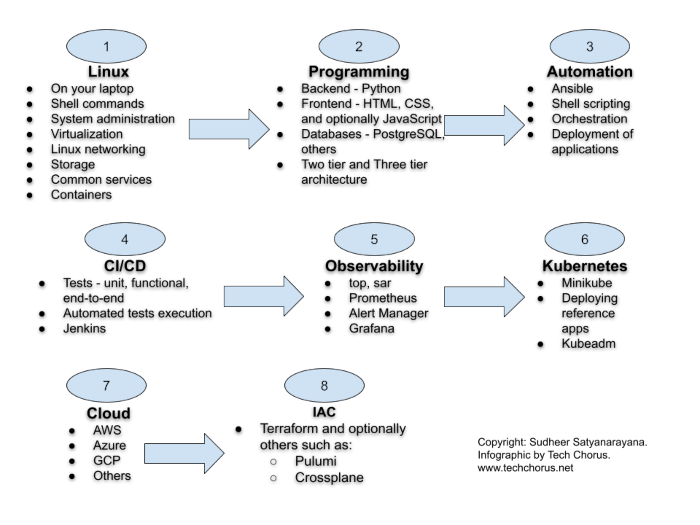
The DevOps Path
- Learn Linux. Install Linux on your laptop. Get familiar with Linux commands. Learn virtualization. Unlock the path to learn more Linux.
- Programming. Acquiring some programming skills using a general purpose programming language like Python goes a long way. Learning some web development is required in most DevOps engineering contexts. Although you don’t have to be an expert in web development, you should have a clear understanding of workloads consisting of web applications and microservices. Learning some HTML, CSS and JavaSript is required for web development. At this point, you have to learn at least one database system. I recommend PostgreSQL to get started with relational database system. Git is also an essential tool to manage source code.
- Automation is the cornerstone of DevOps engineering. Learn the basics of automation with Ansible and shell scripting.
- CI/CD. The purpose of DevOps is to create a culture and practice where developers can ship their applications
to customers quickly, safely and continuously. The
CI/CDpipelines often constitute the backbone of the DevOps practice. Jenkins is a popular tool to createCI/CDpipelines. Learn the basics of Jenkins and create pipelines to automatically test and deploy applications. - Observability and monitoring. Start with Linux commands such as
top,free,duand progress towards Prometheus. The typical Prometheus stack includes Alert Manager and Grafana. Then explore the world of traces with tools such as Jaeger and OpenTelemetry. - Kubernetes. The quintessential container orchestration platform.
- Cloud engineering. Start with one of the popular clouds such as
AWS,AzureorGCP. - IAC. Take automation to the next level in the cloud. Use Terraform to orchestrate resources in the cloud.
Tech Chorus References
- Learning Linux For Devops
- Preparing For A DevOps Engineer Job With A Personal Project
- Three Day Plan To Learn Git
Learning Resources
DevOps
- Coursera Course: Google IT Automation with Python Professional Certificate
- Crash Course On Python
- Using Python to Interact with the Operating System
- Introduction to Git and GitHub
- Troubleshooting and Debugging Techniques
- Configuration Management and the Cloud
- Automating Real-World Tasks with Python
Python
- Free interactive Python tutorial: LearnPython.org
DevOps Lab: Run Your Own DNS Server
As soon as you are ready to deploy services and applications on the Internet, the first thing you need is a registered domain and a DNS server. Often people just use the DNS service provided by the domain registrar or the hosting or cloud provider. Using the managed service is not a requirement. You can host your own DNS server and manage the DNS for your domains. There are many open source software using which you can build your own DNS servers. Bind is the traditional and probably the most popular DNS solution out there. There are other options such as Knot, PowerDNS and Unbound.
Sysctl
Introduction
The Linux Kernel parameters are settings that can be configured to control the behavior of the Linux kernel. They are typically used to fine-tune system performance or to enable/disable certain features.
Some examples of kernel parameters include:
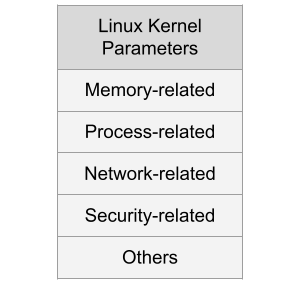
Memory-related parameters: These parameters control how the kernel manages system memory, including how much memory is allocated to user processes and how aggressively the kernel caches data.
Processor-related parameters: These parameters control how the kernel interacts with the system’s processors, including how it schedules processes and how it handles interrupts.
Web Application Ideas Suitable For Beginner Web Developers

The List Of Web Application Ideas
- An e-commerce platform where people can buy and sell products online.
- A platform for booking and managing doctor’s appointments.
- A social networking site for connecting with friends and family.
- A task and project management tool for teams and organizations.
- A recipe and meal planning app for people who want to eat healthy.
- A travel planning and booking app that helps people plan their trips and find the best deals on flights and accommodations.
- An online education platform that offers courses and tutorials on a variety of subjects.
- A fitness and workout tracker that helps users set goals, track their progress, and stay motivated.
- A budgeting and personal finance app that helps people manage their money and save for the future.
- A to-do list and productivity app that helps users organize their tasks and get things done.
Some Common Features Of These Applications
- User accounts and authentication, so users can create an account and log in to the app.
- A user-friendly interface that is easy to navigate and use.
- Search and filtering tools, so users can find what they are looking for quickly and easily.
- Support for different devices and browsers, so users can access the app from any device with an internet connection.
- Social sharing and collaboration features, so users can share content and work together on projects.
- Security measures to protect user data and keep it safe from unauthorized access.
- Analytics and reporting tools to help users track their progress and make data-driven decisions.
- Integration with other tools and platforms, such as payment processors or email marketing services.
- Support for multiple languages and localization, so users can use the app in their native language.
- Responsive design that adjusts to different screen sizes and resolutions, so the app looks good on any device.
Programming Languages, Tools And Technologies
- HTML, CSS, and JavaScript for creating the user interface and front-end of the web application.
- Server-side languages such as Python, Java, or Go for handling the back-end logic and data processing.
- Databases such as MySQL, PostgreSQL for storing and managing data.
- Web frameworks such as Django or
Express.jsfor building the application and handling common web development tasks. - Libraries and tools such as ReactJS or Angular for creating interactive and dynamic user interfaces.
- Git for source control.
- Cloud services such as Amazon Web Services or Google Cloud Platform for hosting the application and supporting its infrastructure.
- Payment processing APIs and integrations for enabling transactions and handling payments.
- Email marketing and messaging APIs for sending notifications and updates to users.
- Analytics and tracking tools for gathering data and generating reports.
- Security tools and practices for protecting user data and ensuring the security of the application
References
Jenkins And Ansible: A Get Together
If you are wondering how to automate the installation and configuration of Jenkins using code, this post is for you.
Jenkins is a popular open source tool to build CI/CD pipelines.
Ansible is a popular open source tool to automate a lot of things in IT, including CI/CD and infrastructure orchestration.
Ansible can be used to deploy applications in the cloud. Ansible is a nice tool to execute steps such as:
Preparing For A DevOps Engineer Job With A Personal Project
The blog post attempts to answer some questions like:
- How to become a DevOps engineer?
- How to prepare for a DevOps engineer interview?
- How to get a DevOps engineer job?
In a previous blog post, I wrote about the path an aspiring DevOps engineer could follow.
In this blog post, I will lay out a concrete plan using which you can prepare yourself for a DevOps engineer job. If you follow the steps carefully, you will be armed with practical DevOps knowledge, and you will be able to apply for DevOps engineer jobs confidently.
Should You Maintain A Private Fork Of Open Source Terraform Modules?
This is a blog post in IAC with Terraform series.
IAC stands for Infrastructure As Code. Modern IT infrastructure can be orchestrated using programmatic methods. Terraform is(was?) a popular open source software used to orchestrate infrastructure in the cloud and elsewhere too.
Terraform has the concept of modules. With modules, you can code abstract infrastructure. For example, if you are creating a pattern of infrastructure over and over again, you could abstract the pattern into a Terraform module. Let’s take the example of a web application. It consists of:
From Build And Deploy Engineer To DevOps Engineer
The build and deploy engineer is a role in IT/infrastructure/devops teams of organizations that is responsible for deploying a set of applications using CI/CD pipelines. Usually, they use the pipelines, tools and processes created by DevOps engineers, consultants or practitioners. They tweak things with tools like Ansible, Jenkins, Git, Maven, etc. here and there a bit.
Are you one such build and deploy engineer looking to transition your career into DevOps engineering? Here’s a path you could follow:
Tech Chorus Blog Hosting Story
The Tech Chorus blog, started by Sudheer Satyanarayana in 2008, has evolved through various hosting technologies and software over the years. This post captures that journey, highlighting the transitions, challenges, and decisions that shaped its infrastructure.
The Early Days: Drupal and LAMP
Back in the day, the blog ran on the Drupal content management system (CMS), a popular choice among developers. The LAMP (Linux, Apache, MySQL, PHP) stack dominated web hosting at the time, and Drupal was one of my favorite CMSes. The site was hosted on a cPanel server, making management relatively straightforward.